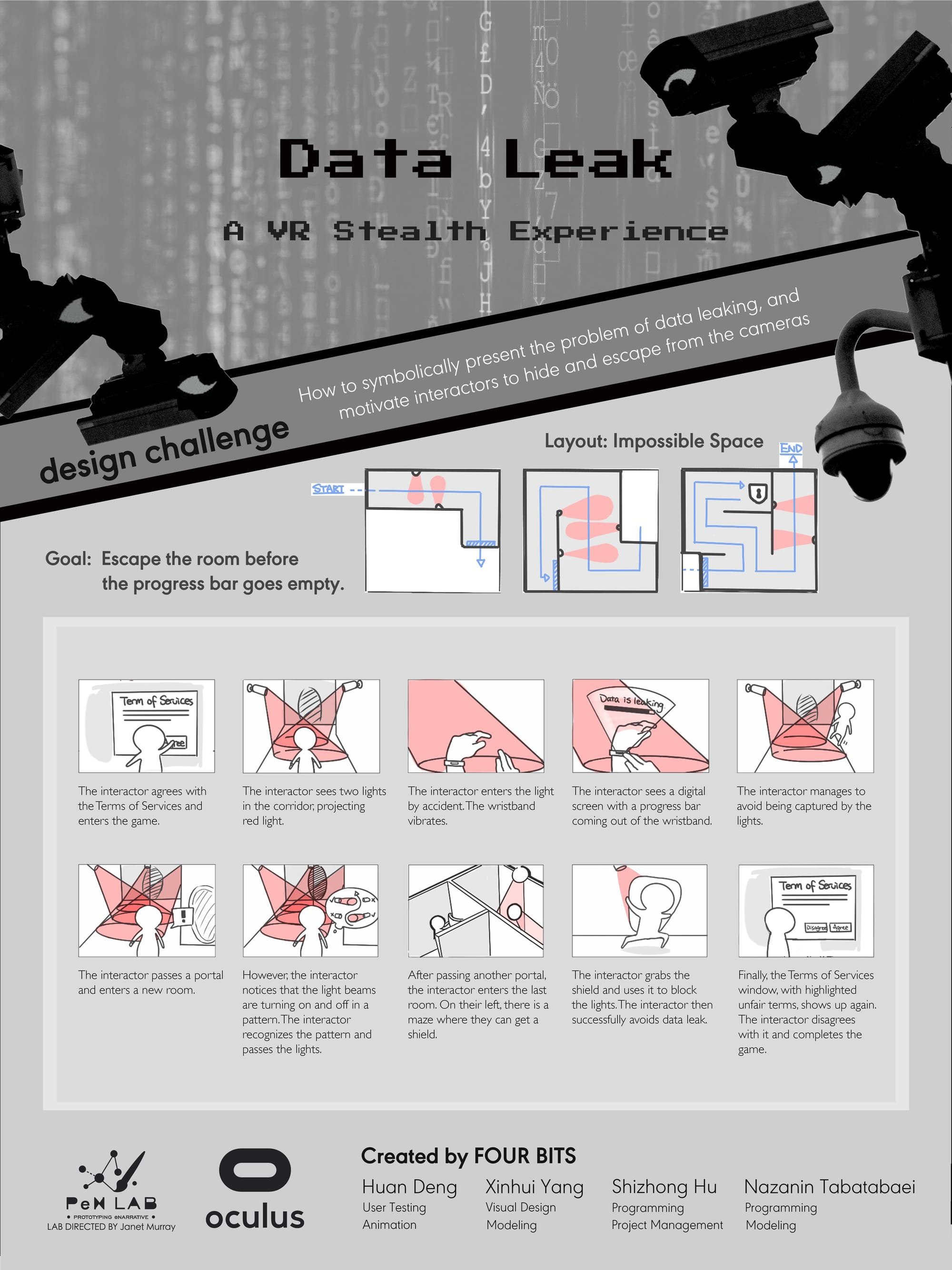
Data Leak
Data Leak is a VR stealth game, designed for Oculus Rift and other room-scale VR devices. The game explores how to symbolically present the problem of data leak and use diegetic methods to cue interactors to avoid data breach. In our game, we incorporate the idea of impossible space by creating different layout in each room and adding a transition portal between the rooms to maximize the physical space.
Data Leak is a VR stealth game, designed for Oculus Rift and other room-scale VR devices. The game explores how to symbolically present the problem of data leak and use diegetic methods to cue interactors to avoid data breach.
As the game starts, the interactor sees the terms of services with blurry sentences and has to agree with it to proceed to the game.
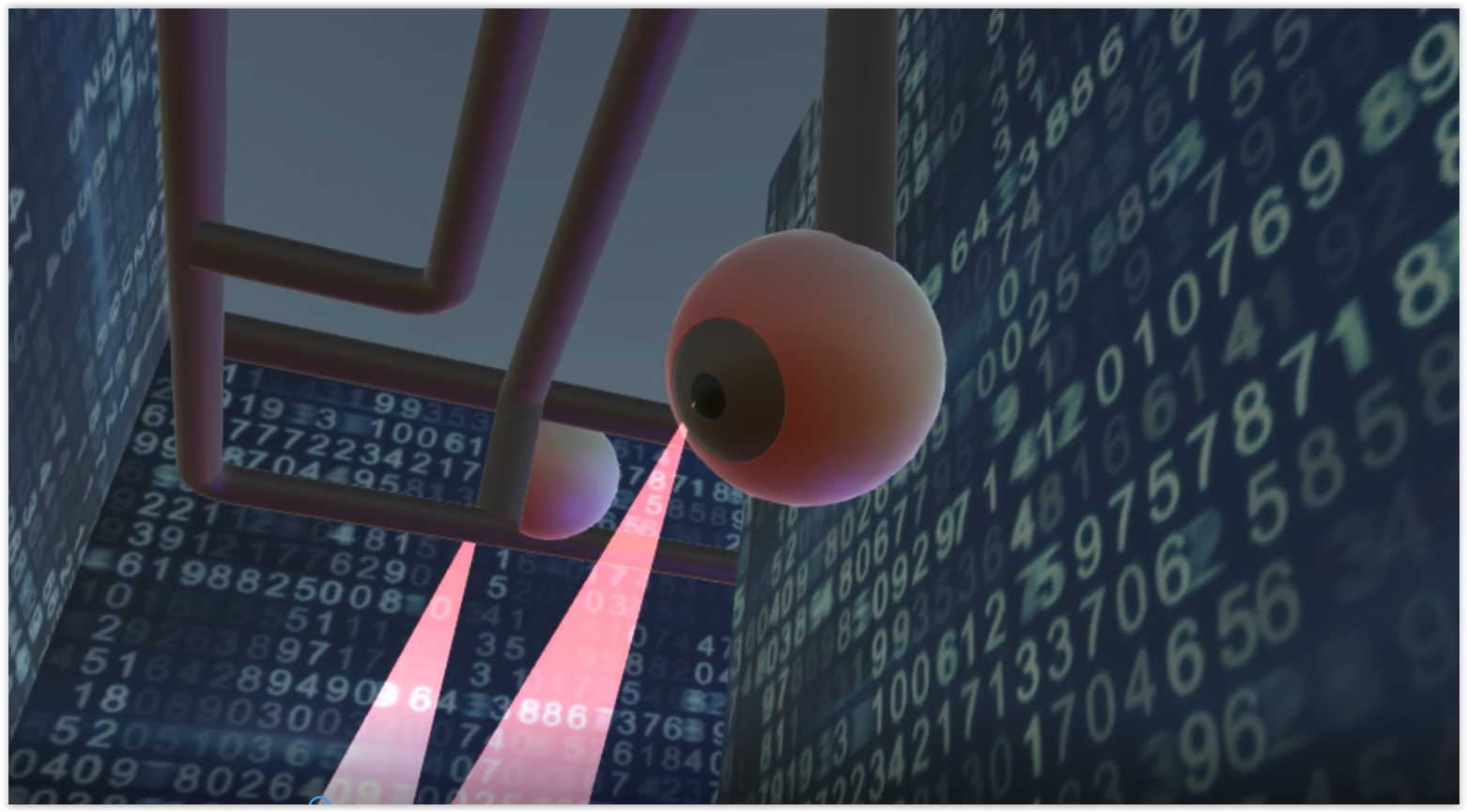
The interactor looks around the futuristic environment with digits on the wall, and sees two lights shooting from the eyeballs, a metaphor of surveillance.
As the interactor tries to touch the light, their action triggers siren and vibration on their hand. “Oh! Data’s Leaking!” The progress bar represents that the interactor’s data is slowly stolen by the light source. The interactor has to avoid the lights and escape the room to prevent the data leaking.
When the interactor approaches the corner, they will see a portal. Passing through it will bring them to a new room. Here we incorporate the idea of impossible space by creating different layout in each room and adding a transition portal between the rooms to maximize the physical room. As the interactor moves through the portal, they shift the virtual space. The mechanism is hidden from the interactor, creating an illusion of a large and consistent virtual space. We created three rooms and used impossible space twice. After passing the second room full of flashing lights, the interactor enters the last room. However, it seems that the lights are too dense, leaving little space to sneak through them. The interactor needs to find another way. Finally the interactor moves around and finds a shield, grabs it up which will make them safe. The design of the shield intends to show the metaphor of information encryption. As interactors bring it back to the lights, they can use it to block the dangerous lights and pass to the final portal safely.
Then the interactor sees the terms of services again. But this time, the previously blurred terms are highlighted. “Your data will be acquired by the game developers. Will you agree this time?”
If the interactor chooses “disagree”, they will succeed the game.
Hopefully, our game can help interactors realize the pervasiveness of data leak and the importance of encryption. We hope to further explore the topic and method in other VR and AR experience.